What we still don’t know about the disastrous Twitter breach

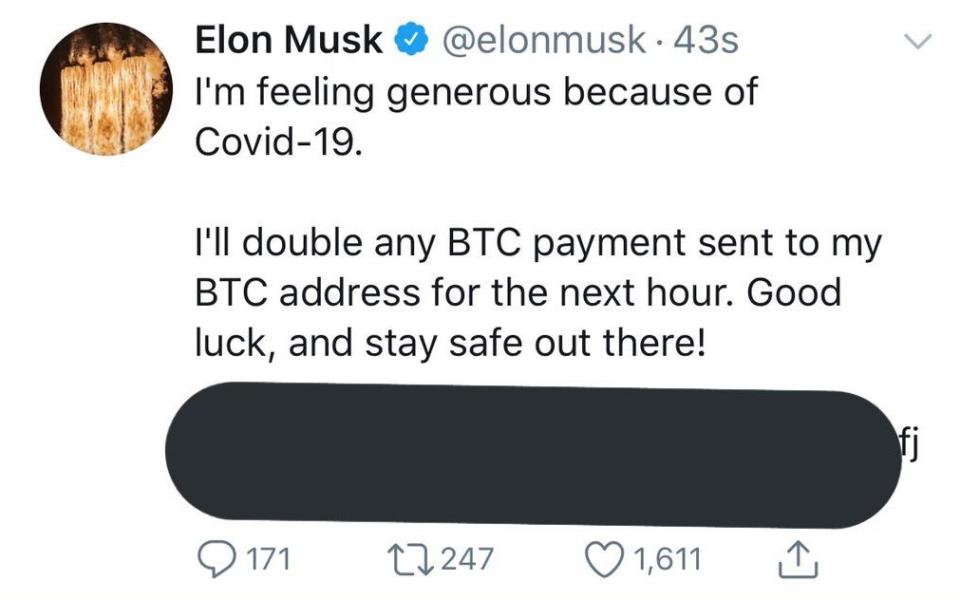
On Wednesday night, Twitter was struck by an unprecedented hack which saw scores of high-profile accounts, from Barack Obama and Joe Biden to Elon Musk and Kayne West, compromised.
But, whilst it is clear that ultimately hackers managed to hijack internal Twitter systems and tools to gain access to “verified” accounts and promote their classic bitcoin scam, details of the breach still remain murky.
As Twitter embarks on an investigation into what happened, here are some of the questions that still need answering:
How exactly did the hackers gain access to the Twitter system?
In the wake of the attack, Twitter signalled its systems had some role to play, saying it has taken “significant steps to limit access to internal systems and tools” while it continued its investigation. It said there had been a “coordinated social engineering attack by people who successfully targeted some of our employees with access to internal systems and tools”.
“We know they used this access to take control of many highly-visible (including verified) accounts and Tweet on their behalf.”
Much speculation, though, has centred on exactly how hackers gained access to these tools, which could be used to control the accounts of some of the most followed people on their site.
One potential answer is that Twitter has shifted many of its staff to remote working – and the increased risks this brings. A survey from security firm Exabeam out this week suggested that 74pc of companies had experienced “slightly to considerably more” cyberattack attempts since the Covid-19 outbreak.
“Companies are grappling with the security fallout from an unexpected shift to remote work, but it’s business as usual for cybercriminals and foreign adversaries with unprecedented opportunity,” Steve Moore, the chief security strategist at Exabeam said.
Yet, in this latest hack, others claimed there was a far simpler answer: that the hackers paid a Twitter employee. Motherboard, a website owned by Vice, cited leaked screenshots in which hackers alleged they had used an employee that “literally done all the work for us”. Twitter told Motherboard it was still investigating whether or not an employee hijacked the accounts themselves or gave the hackers access to the tools.
We detected what we believe to be a coordinated social engineering attack by people who successfully targeted some of our employees with access to internal systems and tools.
— Twitter Support (@TwitterSupport) July 16, 2020
This would not be the first time Twitter has had to deal with talk of rogue employees. In 2017, one of its customer support employees deleted President Donald Trump’s account on their last day, sparking concern among security experts. Twitter later launched an internal review.
Meanwhile, last November, two ex-employees were charged with spying for Saudi Arabia. At the time, the company said it “recognised the lengths bad actors will go to try and undermine our service” and that it “understands the incredible risks faced by many who use Twitter to share their perspectives with the world and to hold those in power accountable”.
Why was Donald Trump not a target?
Almost all those targeted in the attack were “verified” users, meaning they had blue ticks next to their names and were well-known names or brands. But, what is not clear is why particular accounts were chosen over others.
By and large, it appears the hackers were going after accounts with large followings or those with connections to cryptocurrency. Clearly, such a move would likely cause the largest response, and potentially lead to the most money being distributed into the bitcoin wallets.
Yet, the question remains: why were names such as Kanye West and Elon Musk hacked over names like Donald Trump, who has more followers than both combined? Why did Lady Gaga and Taylor Swift escape the hack, over Wiz Khalifa, who has less than half their following?
Some may argue it is down to the security of those accounts, but bitcoin billionaire Cameron Winklevoss says this is not the case.
On Twitter on Wednesday night, he wrote that the account for his company Gemini, which also fell victim to the attack, had been equipped with two-factor authentication and a strong password. Twitter’s investigation may shed some light on what happened.
Is there more to come?
The aim of the attack appears to have been to get users to put cash into a bitcoin wallet – although how successful that was remains unclear. Reports suggested just over $100,000 had been deposited into the accounts on Wednesday evening, but many cyber-criminals also put their own money into the wallet to make the scheme seem legitimate.
However, it is not yet clear if this is the end. After all, the hackers appeared able to gain control of many high-profile accounts, which could mean their private messages and data could have been compromised.
Max Heinemeyer, the director of threat hunting at cyber firm Darktrace, said the “perpetrators may be financially motivated and conducting a smash-and-grab attack, but that does not mean the damage done ends with the bitcoin scam”.
“While Twitter put all hands-on-deck to deal with prominent individuals’ accounts, it is unclear what other nefarious activities the attackers have done behind the scenes – e.g. stealing direct messages between high-profile individuals to use them later for extortion or other crime,” he warned.

 Yahoo Finance
Yahoo Finance 